As the implementation date of the Securing the Information and Communications Technology and Services Supply Chain Interim Final Rule, published in late January and currently effective starting March 22, 2021, approaches, the new White House administration is working to review the legislation and determine if the cost and burden to industry is too great for the rule as it is written. ICTS companies should consider submitting comments to highlight the ways in which the existing rule may be unduly burdensome as written.
WHAT IS SECURING THE ICTS SUPPLY CHAIN RULE?
The Securing the Information and Communications Technology and Services Supply Chain Interim Final Rule creates processes and procedures that the Secretary of Commerce will use to identify, assess, and address certain transactions, including classes of transactions, between U.S. persons and foreign persons that involve information and communications technology or services designed, developed, manufactured, or supplied, by persons owned by, controlled by, or subject to the jurisdiction or direction of a foreign adversary; and pose an undue or unacceptable risk.
The purchase, incorporation, and use by U.S. persons of ICTS—such as network management or data storage—produced by any person owned by, controlled by, or subject to the jurisdiction or direction of a foreign adversary—can create multiple opportunities for those foreign adversaries to exploit potential vulnerabilities in the ICTS.
That, in turn, could cause direct and indirect harm to both the immediate targets of the adverse action and to the United States as a whole. While attacks can originate from remote foreign sources, incorporating certain software, equipment, and products into U.S. domestic ICTS networks, as well as the use of certain cloud, network management, or other services, greatly increases the risk that potential vulnerabilities may be introduced, or that vulnerabilities may be present without being detected.
These potential vulnerabilities, if exploited, could undermine the confidentiality, integrity, and availability of U.S. person data including personally identifiable information or other sensitive personal data.
Examples provided in the Center for Strategic & International Studies, “Significant Cyber Incidents 2020,” available at https://www.csis.org/programs/technology-policy-program/significant-cyber-incidents.
The Secretary has determined that the following foreign governments or foreign non-government persons have engaged in a long-term pattern or serious instances of conduct significantly adverse to the national security of the United States or security and safety of United States persons and, therefore, constitute foreign adversaries solely for the purposes of the Executive Order, this rule, and any subsequent rule:
(1) The People’s Republic of China, including the Hong Kong Special Administrative Region (China);
(2) Republic of Cuba (Cuba);
(3) Islamic Republic of Iran (Iran);
(4) Democratic People’s Republic of Korea (North Korea);
(5) Russian Federation (Russia); and
(6) Venezuelan politician Nicolás Maduro (Maduro Regime).
In the Regulatory Impact Analysis, the U.S. Department of Commerce estimates the number of affected entities that import a significant amount of goods and services potentially subject to review under the rule to be between 268,000 and 4,533,000 firms. The report also approximates the aggregate annualized cost of education, development, implementation, and compliance of the ICTS Supply Chain rule could range from $210 million to $20 billion.
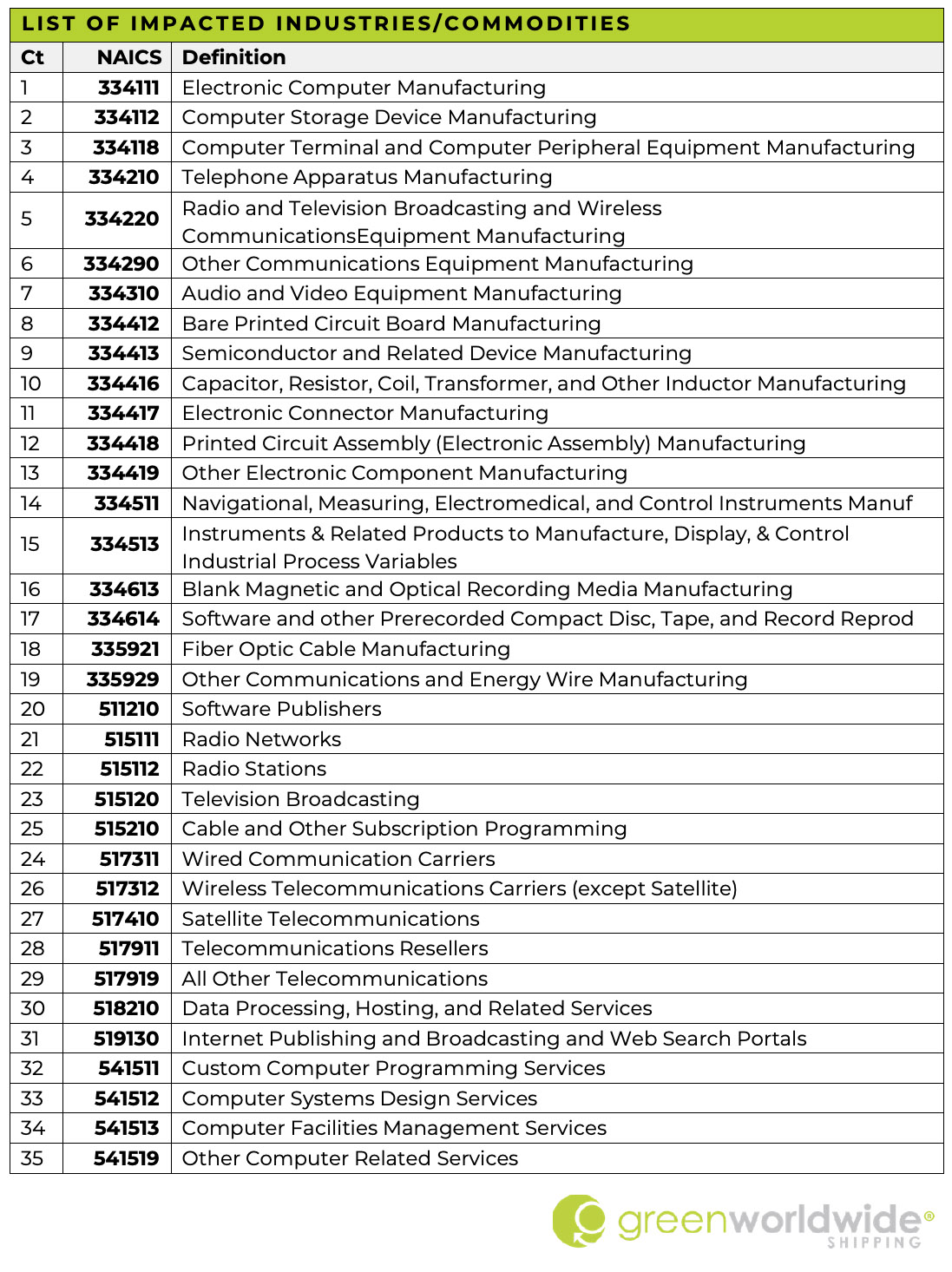
The DOC identified 35 ICTS sectors that include industries likely affected by the rule, below listed by NAICS code:
WHAT IS CONSIDERED AN ICTS TRANSACTION?
(i) ICTS that will be used by a party to a transaction in a sector designated as critical infrastructure by Presidential Policy Directive 21—Critical Infrastructure Security and Resilience, including any subsectors or subsequently designated sectors;
(ii) Software, hardware, or any other product or service integral to:
(A) Wireless local area networks, including:
(1) Distributed antenna systems; and
(2) Small-cell or micro-cell base stations;
(B) Mobile networks, including:
(1) eNodeB based stations;
(2) gNodeB or 5G new radio base stations;
(3) NodeB base stations;
(4) Home location register databases;
(5) Home subscriber servers;
(6) Mobile switching centers;
(7) Session border controllers; and
(8) Operation support systems;
(C) Satellite payloads, including:
(1) Satellite telecommunications systems;
(2) Satellite remote sensing systems; and
(3) Satellite position, navigation, and timing systems;
(D) Satellite operations and control, including:
(1) Telemetry, tracking, and control systems;
(2) Satellite control centers;
(3) Satellite network operations;
(4) Multi-terminal ground stations; and
(5) Satellite uplink centers;
(E) Cable access points, including:
(1) Core routers;
(2) Core networks; and
(3) Core switches;
(F) Wireline access points, including:
(1) Access infrastructure datalinks; and
(2) Access infrastructure digital loops;
(G) Core networking systems, including:
(1) Core infrastructure synchronous optical networks and synchronous digital hierarchy systems;
(2) Core infrastructure dense wavelength division multiplexing or optical transport network systems;
(3) Core infrastructure internet protocol and internet routing systems;
(4) Core infrastructure content delivery network systems;
(5) Core infrastructure internet protocol and multiprotocol label switching systems;
(6) Data center multiprotocol label switching routers; and
(7) Metropolitan multiprotocol label switching routers; or
(H) Long- and short-haul networks, including:
(1) Fiber optical cables; and
(2) Repeaters;
(iii) Software, hardware, or any other product or service integral to data hosting or computing services, to include software-defined services such as virtual private servers, that uses, processes, or retains, or is expected to use, process, or retain, sensitive personal data on greater than one million U.S. persons at any point over the twelve (12) months preceding an ICTS Transaction, including:
(A) Internet hosting services;
(B) Cloud-based or distributed computing and data storage;
(C) Managed services; and
(D) Content delivery services;
(iv) Any of the following ICTS products, if greater than one million units have been sold to U.S. persons at any point over the twelve (12) months prior to an ICTS Transaction:
(A) Internet-enabled sensors, webcams, and any other end-point surveillance or monitoring device;
(B) Routers, modems, and any other home networking device; or
(C) Drones or any other unmanned aerial system;
(v) Software designed primarily for connecting with and communicating via the internet that is in use by greater than one million U.S. persons at any point over the twelve (12) months preceding an ICTS Transaction, including:
(A) Desktop applications;
(B) Mobile applications;
(C) Gaming applications; and
(D) Web-based applications; or
(vi) ICTS integral to:
(A) Artificial intelligence and machine learning;
(B) Quantum key distribution;
(C) Quantum computing;
(D) Drones;
(E) Autonomous systems; or
(F) Advanced Robotics.
WHAT ARE THE IMPORTANT DATES FOR THE ICTS RULE?
Final Rule Effective Date: March 22, 2021
Postponement: Under the new White House administration, a 60-day postponement of the effective date for any rules that have been published in the Federal Register but have not yet taken effect and a 30-day comment period; however, for the ICTS rule, this would result in the same effective date as the original rule, March 22, 2021.
Article Sources:
Regulatory Impact Analysis & Final Regulatory Flexibility Analysis, Department of Commerce, Posted Feb 16, 2021, [DOC-2019-0005-0074] full report is available at https://www.regulations.gov/document/DOC-2019-0005-0074
Final Rule: Securing the Information and Communications Technology and Services Supply Chain, Docket No. 210113-0009 can be found at https://www.federalregister.gov/documents/2021/01/19/2021-01234/securing-the-information-and-communications-technology-and-services-supply-chain
The Center for Strategic & International Studies, “Significant Cyber Incidents 2020” is available at https://www.csis.org/programs/technology-policy-program/significant-cyber-incidents;
The National Security Strategy of the United States is available at https://www.whitehouse.gov/wp-content/uploads/2017/12/NSS-Final-12-18-2017-0905.pdf;
ODNI’s 2016-2019 Worldwide Threat Assessments of the U.S. Intelligence Community are available athttps://www.dni.gov/files/documents/Newsroom/Testimonies/SSCI%20Unclassified%20SFR%20-%20Final.pdf(2017), https://www.dni.gov/files/documents/Newsroom/Testimonies/2018-ATA—Unclassified-SSCI.pdf(2018), https://www.dni.gov/files/ODNI/documents/2019-ATA-SFR—SSCI.pdf (2019); and
The 2018 National Cyber Strategy of the United States of America is available at https://www.whitehouse.gov/wp-content/uploads/2018/09/National-Cyber-Strategy.pdf.
As Green continues to monitor the situation, stay up-to-date on freight news by following us on Facebook, Twitter, and LinkedIn. For continuous updates, make sure to check out our website at greenworldwide.com.
IMPORTERS & EXPORTERS NEED A RELIABLE COMPLIANCE PARTNER TO GUIDE THEM THROUGH THIS REGULATORY MAZE
meet kate rayer
Global Trade Manager, LCHB
Green Worldwide Shipping, LLC